Background
The Onion Router (Tor) Browser is a free, open-source web browser designed as a Privacy Enhancement Tool (PET) for anonymous communication and online privacy. The Tor network routes traffic through a series of volunteer-operated proxy servers (known as relays or nodes, forming a complete "circuit") to conceal a user's location and usage from classical surveillance and traffic analysis (The Tor Project Inc., 2025).
The browser is developed by "The Tor Project", a 501(c)(3) U.S nonprofit, initially created in the mid-1990s by U.S naval researchers to protect government communications, before being released publicly as open-source software in October 2002 to "advance human rights and defend your privacy online through free software and open networks" (The Tor Project Inc., 2025).
As an open-source nonprofit, The Tor Project Inc. accepts voluntary contributions through code or funding, with the network itself running through thousands of global volunteer relay operators who donate bandwidth and computing resources (The Tor Project Inc., 2025).
The browser is typically used to circumvent censorship and surveillance, creating an extremely diverse user-base: journalists and whistleblowers, human rights activists in repressive regimes, researchers and ordinary users concerned with privacy, and law enforcement for undercover communications. There are an estimated 2 million daily users worldwide (The Tor Project Inc. Metrics, 2025). Built upon a modified version of Mozilla Firefox, the browser is configured with strong privacy defaults to combat fingerprinting and data leaks, and includes security add-ons (The Tor Project Inc., 2025).
Testing
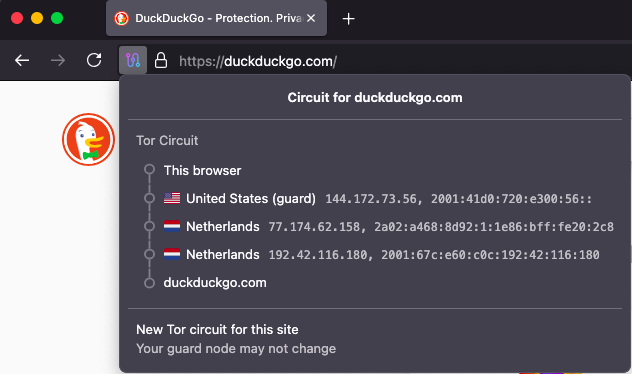
Tor's primary attraction is masking users' identity through a three-layered proxy-server network called an "active circuit", passing data through a Guard, Middle, and Exit node. This can be tested by clicking the circuit icon next to the URL bar in Tor Browser, which shows each relay's IP address, with an option to generate a new circuit.
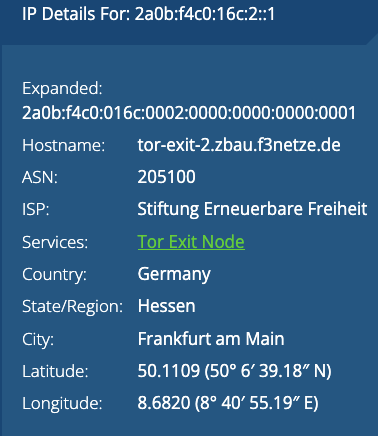
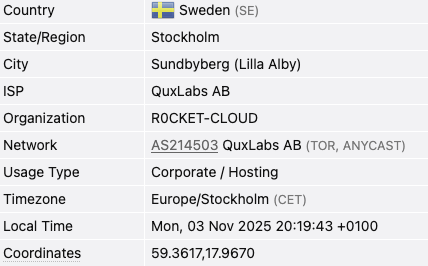
To verify that the active circuit masks the user's visible IP address, I navigated to https://whatismyipaddress.com/ on both Safari (through a standard internet connection) and Tor Browser. In Figures 2 and 3, it can be observed that the IP address and location of Tor Browser's exit node differs from my local network's public IP, and the site additionally recognises the use of a Tor Exit Node.

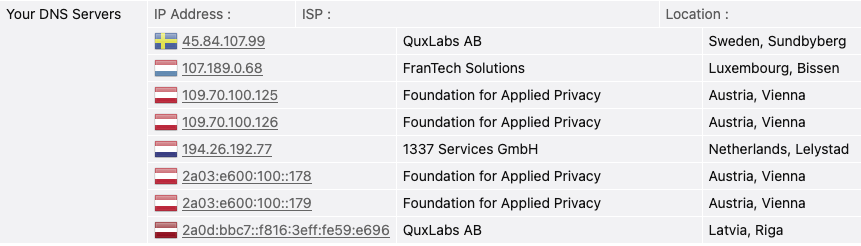
I then performed a DNS leak test (https://browserleaks.com/dns/) to evaluate whether Tor anonymises DNS lookups by ensuring requests are resolved by exit relays instead of the local ISP. In Figures 4 and 5, the DNS is resolved through a range of servers outside of England, identified as Tor exit nodes by the test site.
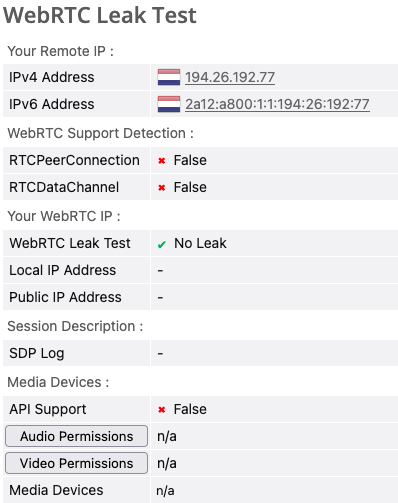
After validating network-layer privacy, I tested for application-layer leaks using a WebRTC test, comparing Safari and Tor Browser. Navigating to https://browserleaks.com/webrtc, Figure 6 shows that Tor Browser does not allow any WebRTC leaks and does not support the media API for audio or video devices.
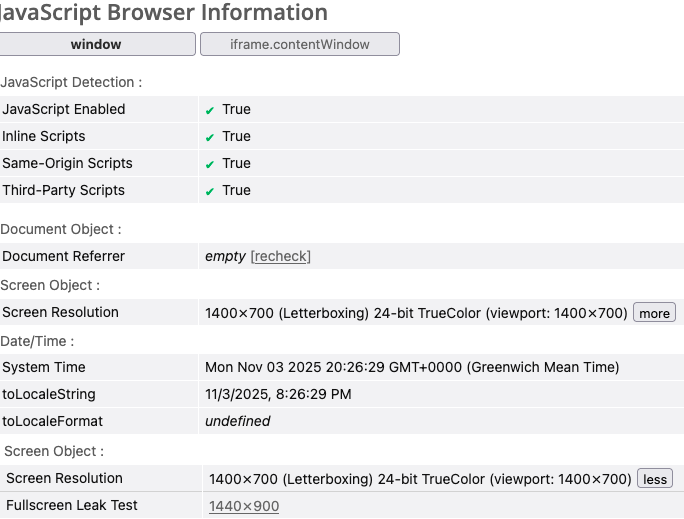
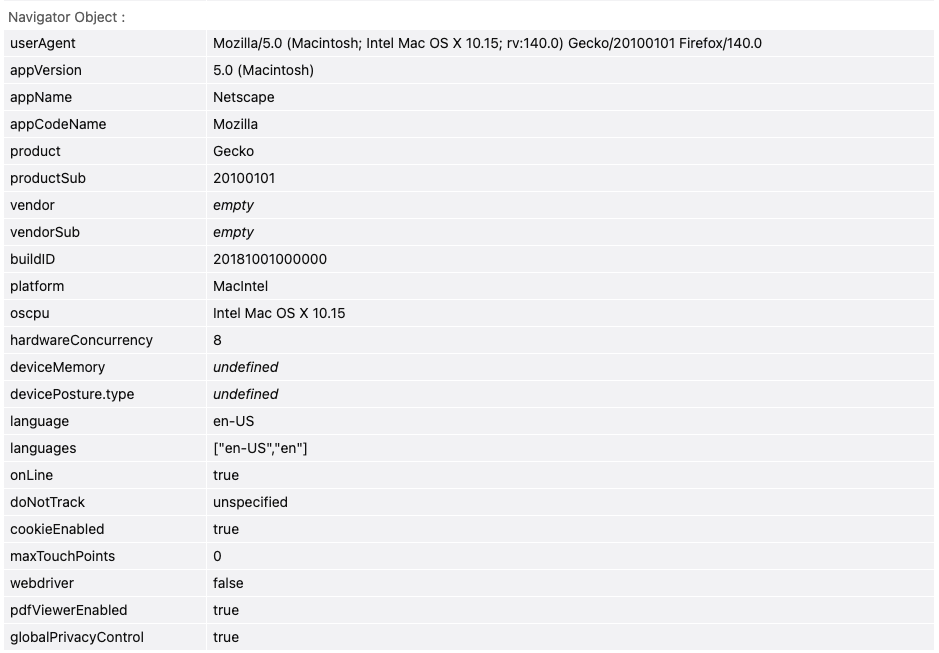
To further evaluate Tor's default privacy configurations, I tested what browser information could be accessed via JavaScript at https://browserleaks.com/javascript. By default, the browser leaks some information about the user's operating system and screen resolution, though the operating system information is not entirely correct (likely related to the CPU architecture of my older Macbook). Additionally, if a user enables fullscreen control of a media container, the exact screen size in pixels becomes accessible — suggesting a user could potentially be physically linked to their digital identity if a host could estimate and verify the device type. While Tor Browser allows JavaScript execution by default (The Tor Project Inc. Gitlab, 2025), limiting this leak appears to require setting Tor's privacy level to "Safest" to disable JS entirely.
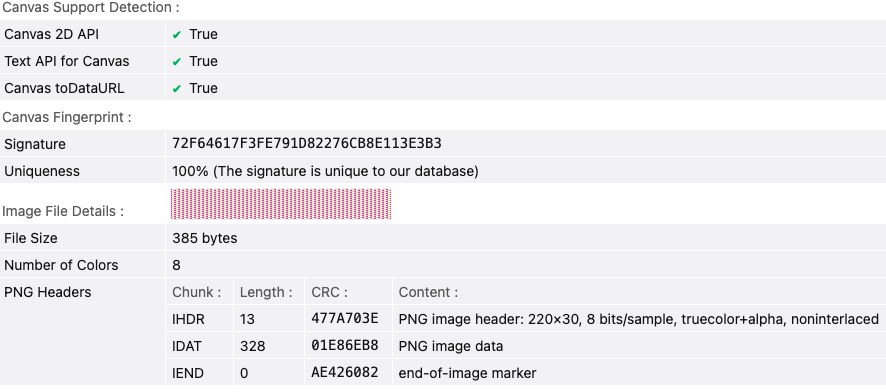
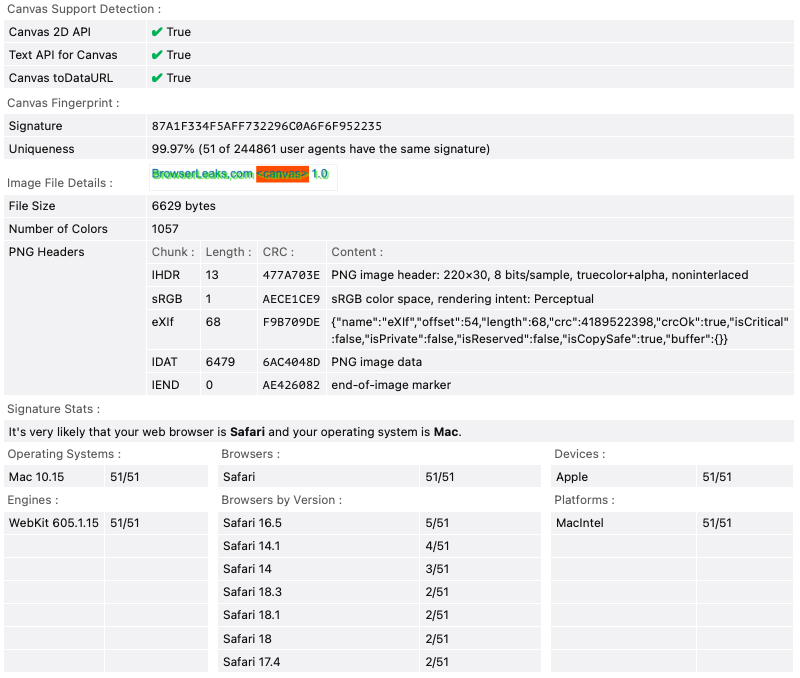
Finally, the previous results suggested it was necessary to test Tor Browser's resistance to fingerprinting (https://browserleaks.com/canvas), a common method of user tracking across browsers (IEEE Spectrum, 2020). As seen in Figure 10, Tor Browser's fingerprint is completely unique among 255,587 other user agents, leaking no identifiable information. In contrast, Safari's (ver. 15.6.1) results in Figure 11 show that 52 other tests have seen the same browser signature.
Analysis of a 'Global Passive Adversary' as a potential misuse or weakness
Despite Tor's global, decentralised network, the design acknowledges it cannot protect against a fully-powerful adversary able to observe all network traffic — known as a Global Passive Adversary (Dingledine, R., Mathewson, N. and Syverson, P., 2004) — and so assumes a typical threat would involve partial node control (Buccafurri, F., De Angelis, V., Idone, M.F., Labrini, C. and Lazzaro, S., 2022). If an adversary could monitor traffic at many or all nodes, traffic entering and leaving could be correlated, compromising anonymity through user linkability (Dingledine, R., Mathewson, N. and Syverson, P., 2004).
Edward Snowden's whistleblowing revealed that the NSA had "made repeated attempts to develop attacks against people using Tor" (The Guardian, 2013), acting as a global passive adversary by observing national traffic without actively interfering with data. Such an adversary can exploit Tor's lack of cover traffic or padding, which would otherwise defeat correlation with nonsense data (Buccafurri, F., De Angelis, V., Idone, M.F., Labrini, C. and Lazzaro, S., 2022). Potential misuse could de-anonymise dissidents or journalists in oppressive states, or track users of hidden services for intelligence purposes. Tor may therefore provide resistant rather than perfect anonymity — effective against adversaries unable to conduct mass surveillance, but not those that can.
Improving upon 'Global Passive Adversary' weaknesses
Preventing any entity from surveilling Tor exit nodes is non-trivial given varying national laws, so it is more feasible to focus on mitigating threats through traffic analysis prevention. As proposed by (Buccafurri et al., 2022), dummy "cover" data could blur timing and volume patterns, making correlation harder. However, the additional latency and bandwidth overhead would degrade performance and user experience, requiring greater relay capacity and physical infrastructure scaling.
Alternatively, improving routing and relay selection could reduce the number of critical nodes observable by a single adversary — for example, avoiding placing entry and exit nodes on paths observable by the same Autonomous System (AS) or national jurisdiction. The TOAR framework proposes an algorithm that "searches for routes that conform to established policies, avoiding AS that could connect traffic [...] maintaining anonymity in the selection of routes that minimise communication costs" (Zhao, H. & Song, X., 2024). Again, client-side route computation increases complexity and may reduce relay efficiency or require additional AS path metadata.
A combination of both approaches could be applied as anonymity set enlargement (k-enlargement), where we "guarantee that an adversary, trying to determine the sender of a particular message, can only narrow down its search to a set of k suspects" (Freedman et al., 2001). Larger anonymity sets, however, require more cover traffic and nodes, creating high costs for a nonprofit open-source project.
Overall, securing Tor is — and always will be — a balance between usability and security. Relay operators may not willingly accept higher overheads, risking damage to the volunteer base, and increased delays could discourage users from an already slow network, reducing the anonymity set and weakening existing security. It is also difficult to know when the threat of GPA is sufficiently mitigated, since recent history shows we may never fully know what surveillance techniques governments employ against us (The Guardian, 2013) — this will continue to be a thoroughly researched topic until a solution preventing contemporary surveillance can be verified.
Reference List
The Tor Project Inc. (2025) Tor Browser – Browser Privately. Explore Freely. Available at: https://www.torproject.org/ (Accessed: 06 November 2025)
The Tor Project Inc. (2025) Tor Browser History Page Available at: https://www.torproject.org/about/history/ (Accessed: 06 November 2025)
The Tor Project Inc. (2025) What is Tor Browser and how does it work? Available at: https://support.torproject.org/tor-browser/getting-started/about-tor-browser/ (Accessed: 06 November 2025)
The Tor Project Inc. Metrics (2025) Tor Metrics Available at: https://metrics.torproject.org/reproducible-metrics.html (Accessed: 06 November 2025)
The Tor Project Inc. Gitlab. (2025) Tor Gitlab – Ticket #26146 Available at: https://gitlab.torproject.org/legacy/trac/-/issues/26146 (Accessed: 06 November 2025)
IEEE Spectrum (2020) Browser fingerprinting and the online-tracking arms race. Available at: https://spectrum.ieee.org/browser-fingerprinting-and-the-onlinetracking-arms-race (Accessed: 06 November 2025)
Dingledine, R., Mathewson, N. and Syverson, P., 2004. Tor: The second-generation onion router. Proceedings of the 13th USENIX Security Symposium. Available at: https://www.cl.cam.ac.uk/~sjm217/papers/tor14design.pdf (Accessed: 06 November 2025)
Buccafurri, F., De Angelis, V., Idone, M.F., Labrini, C. and Lazzaro, S., 2022. Achieving sender anonymity in Tor against the global passive adversary. Applied Sciences, 12(1), p.137. Available at: https://www.mdpi.com/2076-3417/12/1/137 (Accessed 6 November 2025)
The Guardian (2013) NSA and GCHQ target Tor network that protects anonymity of web users Available at: https://www.theguardian.com/world/2013/oct/04/nsa-gchq-attack-tor-network-encryption (Accessed: 06 November 2025)
Zhao, H. & Song, X., 2024. TOAR: Toward Resisting AS-Level Adversary Correlation Attacks Optimal Anonymous Routing. Mathematics, 12(23), 3640. Available at: https://www.mdpi.com/2227-7390/12/23/3640 (Accessed 6 Nov 2025)
Freedman, M.J. & Morris, R., 2001. k-anonymous message transmission. In: Proceedings of the 14th ACM Conference on Computer and Communications Security. ACM Press, pp. 41–48. doi:10.1145/948109.948128. Available at: https://dl.acm.org/doi/abs/10.1145/948109.948128 (Accessed 6 November 2025)